Report Structure
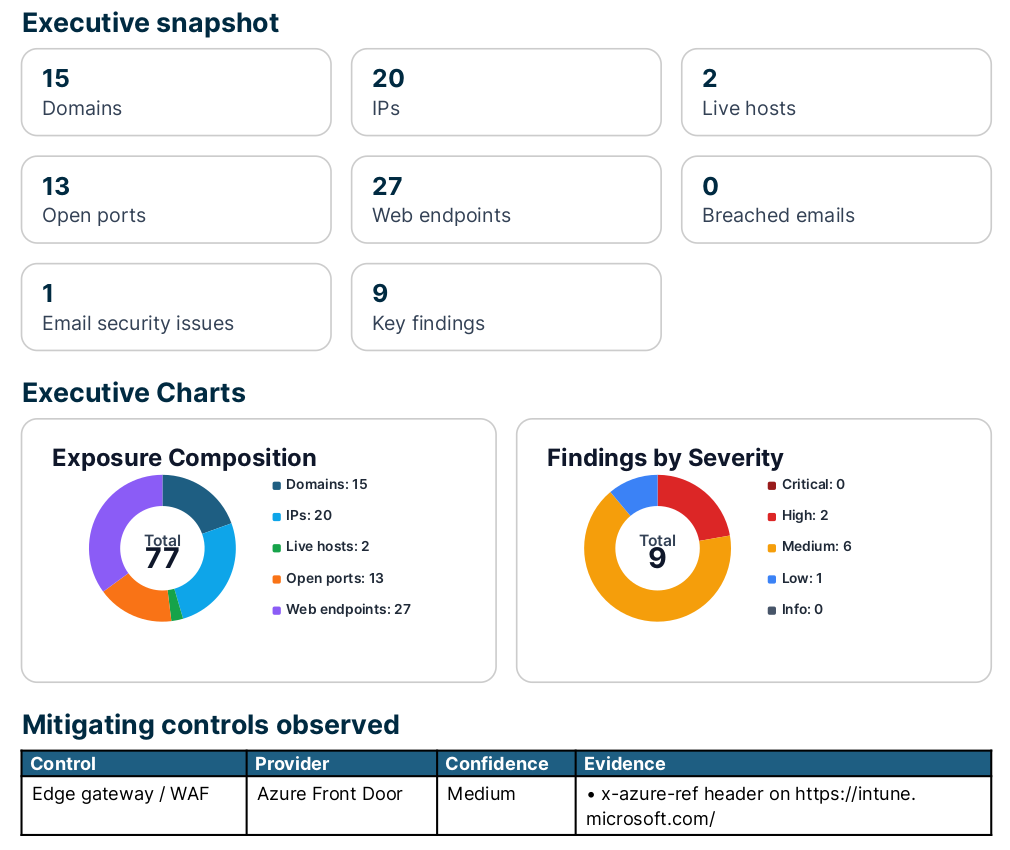
- Executive summary and headline risk score
- External asset inventory (domains, IPs, ports, web endpoints)
- Risk-scored findings with evidence and remediation
- Screenshots of exposed and authenticated admin interfaces
- Web vulnerability scan findings across all live endpoints
- Deep TLS analysis (deprecated protocols, known exploits, weak ciphers)
- JavaScript and public code secret detection
- Email security posture (SPF, DMARC, DKIM)
- CVE correlation and IP reputation results
- Exposure drift tracking against prior scan
- Risk matrix and scoring rationale appendix
Risk Summary Snapshot
Example Findings
| Severity | Finding | Why it matters | Recommended action |
|---|---|---|---|
| Critical | Default credentials accepted on internet-facing services | Grafana, Tomcat Manager, and an FTP server all accepted publicly known default credentials. No prior knowledge required — default credential lists are built into automated attack tooling. | Change default credentials immediately. Restrict management interfaces to internal networks or VPN. Audit each system for signs of prior unauthorised access. |
| Critical | Verified credentials exposed in public source code repository | An active AWS access key and a database password were found in publicly accessible source code commits and confirmed as currently valid. Any actor can use them immediately — no exploitation skill required. | Revoke and rotate all exposed credentials immediately. Remove from repository history. Implement pre-commit secret scanning to prevent recurrence. |
| High | Risky network service publicly reachable | A database or management service (e.g. Redis, RDP) accepts connections from the internet, enabling direct brute force and exploitation attempts. | Restrict access by source IP. Place behind a VPN or bastion. Disable if not required. |
| High | Known CVE correlated to service fingerprint | A publicly documented, CVSS-scored vulnerability matches a service version visible from the internet. Tooled exploits likely exist. | Apply vendor patch. Restrict internet access to the service where patching is not immediately possible. |
| High | Deprecated TLS protocol supported (TLS 1.0) | TLS 1.0 is deprecated and vulnerable to downgrade attacks. PCI-DSS prohibits its use for cardholder data environments. Clients and scanners will negotiate the weakest mutually supported version. | Disable TLS 1.0 and TLS 1.1. Configure the server to support TLS 1.2 and TLS 1.3 only with AEAD cipher suites. |
| High | IP address listed on Spamhaus XBL | The Exploits Block List indicates the IP was observed sending botnet or exploit traffic — a strong indicator of host compromise. | Treat the host as potentially compromised. Investigate, remediate, and request delisting via check.spamhaus.org. |
| Medium | Hardcoded API key in publicly accessible JavaScript | A third-party API key was found embedded in a JavaScript file served to all visitors. Client-side code is fully readable — secrets placed here are exposed to anyone who opens the browser devtools. | Remove the key from the JavaScript file immediately. Rotate the credential and move it server-side. Implement pre-commit secret scanning. |
| Medium | Admin interface publicly reachable | A management panel is exposed to internet scanning and brute-force attempts without network-level access controls. | Place behind VPN or SSO. Enforce MFA and IP allowlisting. |
| Medium | Email spoofing protections absent or misconfigured | Weak SPF and unenforced DMARC allow any host to send email impersonating your domain — the primary enabler of BEC and phishing attacks. | Publish a strict SPF record, set DMARC to p=reject, and configure DKIM signing. |
| Low | TLS certificate expiring within 30 days | An expiring certificate risks service outages and browser trust warnings if not renewed in time. | Renew the certificate and consider automated renewal via Let's Encrypt or your CA's ACME endpoint. |
| Low | Sensitive file accessible at well-known path | A .env file or .git/ directory is publicly readable, potentially exposing credentials, API keys, or source code. | Remove the file from the web root, audit for credential exposure, and rotate any secrets that may have been disclosed. |
Additional Coverage
Included in every scan — hundreds of additional checks run automatically against discovered services.
Web Vulnerability Scan
Hundreds of checks run against every live web endpoint — known CVEs matched to running software, exposed configuration panels, dangerous defaults, and misconfigurations. Each finding is severity-scored with the matched URL and remediation guidance.
- exposed debug interfaces and stack traces
- known CVEs matched to detected service versions
- insecure HTTP methods enabled
- directory listing and path traversal indicators
- exposed Swagger / OpenAPI schemas
TLS Deep Analysis
Every TLS endpoint is audited beyond version and cipher — testing for known exploitable protocol vulnerabilities that a basic scan misses.
- deprecated protocols: SSLv2, SSLv3, TLS 1.0, TLS 1.1
- BEAST, POODLE, Heartbleed, ROBOT
- SWEET32, FREAK, Logjam (weak DH)
- RC4, export-grade, and null ciphers
- anonymous and null authentication suites
JavaScript & Public Code Secrets
JavaScript files loaded by your web endpoints are fetched and scanned. Public source code repositories are searched for commits mentioning your domain.
- AWS, GitHub, Stripe, Slack, SendGrid API keys
- hardcoded passwords and bearer tokens
- private key material
- verified secrets reported as Critical
- internal API paths extracted from JS bundles
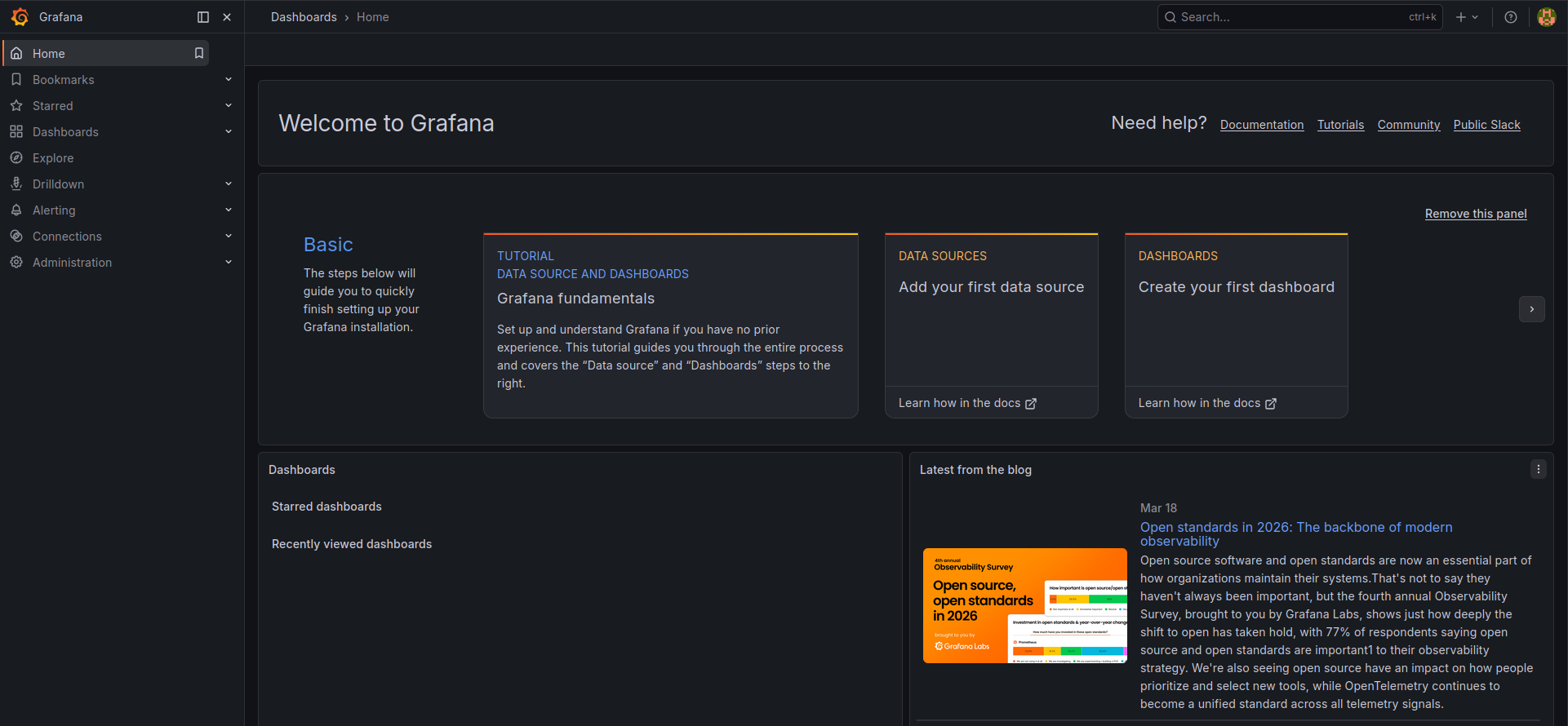
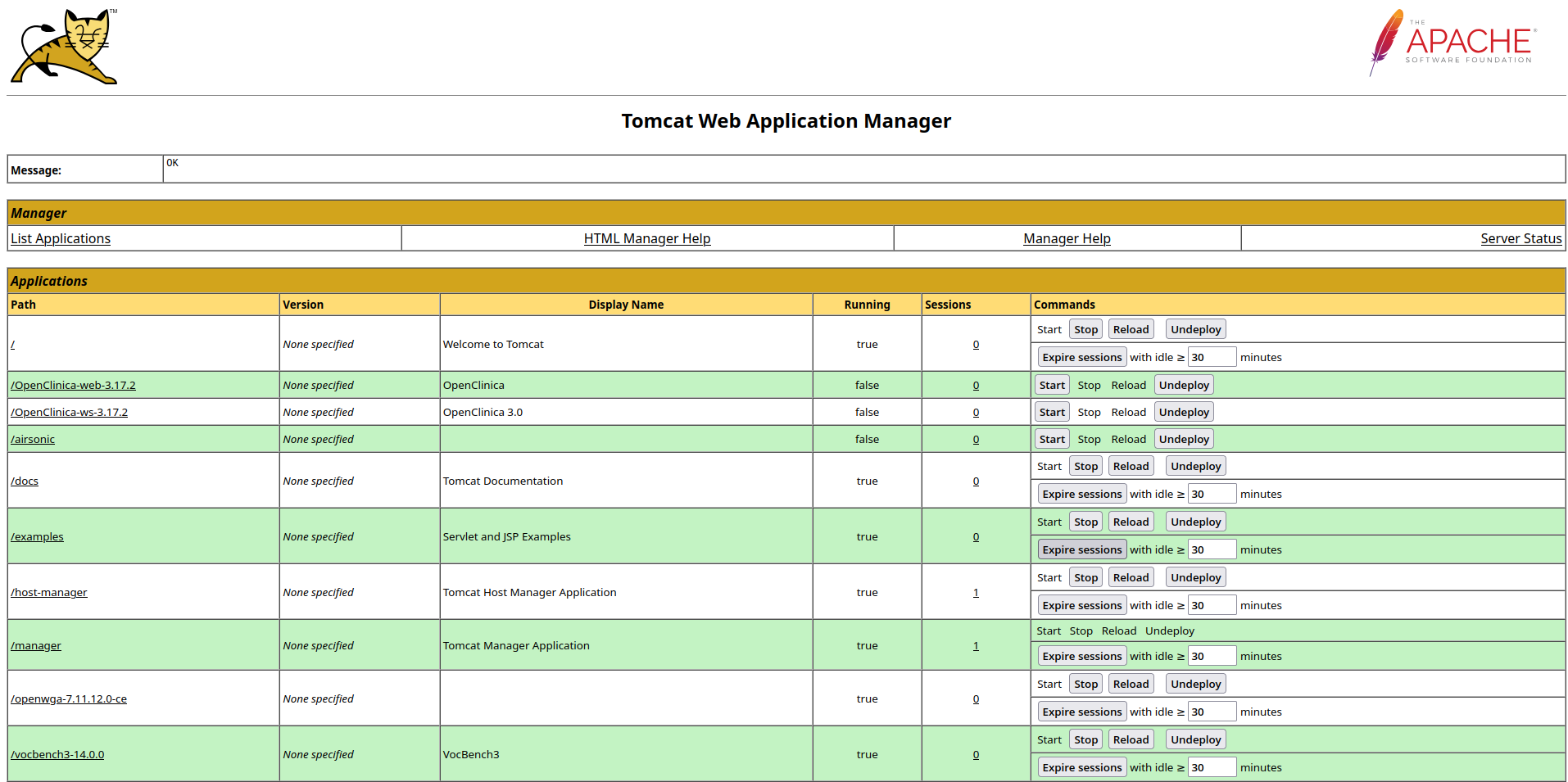
Authenticated Access — Screenshot Evidence
When default credentials are accepted, SurfaceMapper captures the authenticated session as evidence.
Grafana — admin:admin
Tomcat Manager — tomcat:tomcat
FTP — anonymous access
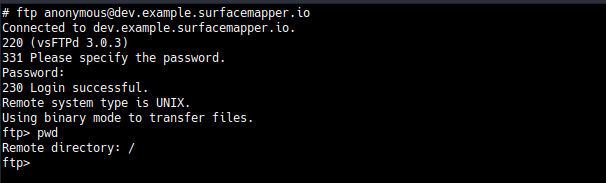
Why this matters
Default credentials are the lowest possible exploitation barrier. Tooling like Metasploit and Shodan-based scanners attempt them automatically within minutes of a service being indexed. A confirmed login means the system is already accessible to any attacker — not just a motivated one.
Default credential testing requires explicit written authorisation from the client, confirmed at the time of scan request.